Risk actors have been leveraging faux web sites promoting standard video conferencing software program similar to Google Meet, Skype, and Zoom to ship quite a lot of malware focusing on each Android and Home windows customers since December 2023.
“The menace actor is distributing Distant Entry Trojans (RATs) together with SpyNote RAT for Android platforms, and NjRAT and DCRat for Home windows methods,” Zscaler ThreatLabz researchers said.
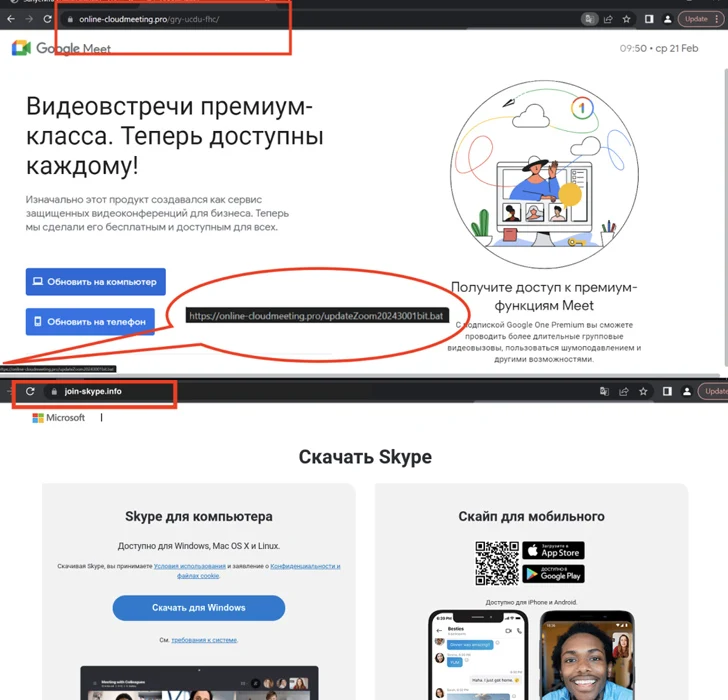
The spoofed websites are in Russian and are hosted on domains that carefully resemble their reliable counterparts, indicating that the attackers are utilizing typosquatting tips to lure potential victims into downloading the malware.
In addition they include choices to obtain the app for Android, iOS, and Home windows platforms. Whereas clicking on the button for Android downloads an APK file, clicking on the Home windows app button triggers the obtain of a batch script.
The malicious batch script is answerable for executing a PowerShell script, which, in flip, downloads and executes the distant entry trojan.
At present, there isn’t a proof that the menace actor is focusing on iOS customers, provided that clicking on the button for the iOS app takes the person to the reliable Apple App Retailer itemizing for Skype.
“A menace actor is utilizing these lures to distribute RATs for Android and Home windows, which may steal confidential data, log keystrokes, and steal recordsdata,” the researchers stated.
The event comes because the AhnLab Safety Intelligence Heart (ASEC) revealed {that a} new malware dubbed WogRAT focusing on each Home windows and Linux is abusing a free on-line notepad platform referred to as aNotepad as a covert vector for internet hosting and retrieving malicious code.
It is stated to be energetic from a minimum of late 2022, focusing on Asian nations like China, Hong Kong, Japan, and Singapore, amongst others. That stated, it is at present not recognized how the malware is distributed within the wild.
“When WogRAT is run for the primary time, it collects fundamental data of the contaminated system and sends them to the C&C server,” ASEC said. “The malware then helps instructions similar to executing instructions, sending outcomes, downloading recordsdata, and importing these recordsdata.”
It additionally coincides with high-volume phishing campaigns orchestrated by a financially motivated cybercriminal actor generally known as TA4903 to steal company credentials and certain observe them with enterprise e mail compromise (BEC) assaults. The adversary has been energetic since a minimum of 2019, with the actions intensifying submit mid-2023.
“TA4903 routinely conducts campaigns spoofing numerous U.S. authorities entities to steal company credentials,” Proofpoint said. “The actor additionally spoofs organizations in numerous sectors together with development, finance, healthcare, meals and beverage, and others.”
Assault chains contain the usage of QR codes (aka quishing) for credential phishing in addition to counting on the EvilProxy adversary-in-the-middle (AiTM) phishing equipment to bypass two-factor authentication (2FA) protections.
As soon as a goal mailbox is compromised, the menace actor has been noticed trying to find data related to funds, invoices, and financial institution data, with the final word objective of hijacking current e mail threads and performing bill fraud.
Phishing campaigns have additionally functioned as a conduit for other malware families like DarkGate, Agent Tesla, and Remcos RAT, the final of which leverages steganographic decoys to drop the malware on compromised hosts.